
Block Management
Transparent repeater
Guest Wifi
Tor Network
OpenVPN
PPTP/L2TP
DDNS
Block Management
What is Block Management ?
- Block Devices Updates can prevent connected devices from automatic system & apps updates when using 3G/4G/LTE or in bandwidth limited connections.
- Block Cloud Storage Syncing can prevent connected devices from syncing with Cloud Storage services.
- Block Blacklist can block publicly reported websites containing advertisement, suspected malicious software and adult contents.
- Custom Websites & Keywords can block websites containing the desired websites or keywords.
This menu allows you to configure if popular phones, tablets or computers are allowed to update their operating systems software or software patches when connected to your EZhotspot Extender.
For example: Operating systems such as IOS can sometimes automatically download as much as 1GB of updates in the background.
| Block Devices Updates | |
| Apple | |
| Android | |
| Amazon Kindle/Fire |
|
| Windows | |
This menu allows you to configure if popular cloud storage applications are allowed to be synced when connected to your EZhotspot Extender.
| Block Cloud Storage Syncing | |
| Amazon Drive | |
| OneDrive | |
| iCloud | |
| Dropbox | |
| Google Drive | |
This menu allows you to configure block blacklisted websites and/or by custom keywords when connected to your EZhotspot Extender.
Transparent Repeater
This menu allows you to configure the Transparent Repeater
Note: You need to first join to a wireless network you want to repeat. Otherwise, you will be prompted to do so
 connect first |
This menu allows you to enter the Transparent Repeater's SSID broadcasted by the EZhotspot Extender.
For example: A different name to differentiate from the home router or repeat using the same SSID as the home router.
 |
Note: On the V5, it is only possible to configure the Transparent Repeater on either the 5Ghz or 2.4Ghz. If you are already repeating on both 5Ghz and 2.4Ghz, you will be prompted to disconnect an existing connection before you are allowed to further proceed in this menu.
Note: The wireless key of the Transparent Repeater is the same as the original home router.
Note: For firmware version 4.12 and below: When you to exit from the Transparent Repeater, press and hold the reset button for 12~15 seconds and the device is back to a factory default, ready to join to a new wireless network.

The Transparent Repeater function creates a transparent wireless bridge to the joined network and allow both wired & wireless clients connecting to the EZhotspot Extender to obtain networking credentials directly from your ADSL/Cable/Fiber Router or DHCP server.
The result is that all devices will appear to be on a single network, making Network Access Storage, File & Printer Sharing, IP cameras, etc; easy to access. The Transparent Repeater is great if you planned on using the EZhotspot EXtender on a long term basis at home to extend the wireless signal of your original wireless router.
The Transparent Repeater does not work on public hotspots requiring portal login, WEP encrypted networks (very outdated & unsafe!) and WPA/WPA Enterprise 802.1x encrypted networks.
Depending on the product with the firmware version and above:
- EZ311-V4 (firmware version 4.48)
- EZ511-V5 (firmware version 5.50)
- Scan and connect to the wireless Google Mesh SSID.
- After a successful connection, go to Special Add-Ons --> Transparent Repeater menu.
- Specify a desired SSID for the EZhotspot to broadcast and confirm to proceed.
- When the countdown completes, the desired SSID with the wireless key (similar to join to the Google Mesh SSID) is broadcasted by the Ezhotspot..
- Any device joining to this new SSID will be assigned an IP address from the Google Mesh network. The device will be on the same subnet mask as other devices joined directly to the wireless Google Mesh network.
Guest Wifi
The menu allows you to configure a wireless Guest SSID.
Guest SSID :
Guest Wireless Encryption :
|
| Guest SSID: | The Guest network to be broadcasted for your guest to find in their devices' wireless settings | |
| Open network which does not requires a wireless key to join | ||
| Secured network which requires a wireless key of minimum 8 characters to join |
This menu allows you to set the wireless key if selected and bandwidth speed assigned to the wireless Guest network
|
|
| A wireless key of minimum 8 characters is required to join | ||
| Maximum download speed : | Default is 2000Kbps / 2Mbps | |
| Maximum upload speed : | Default is 500Kbps / 0.5Mbps |

The Guest Wifi creates a separate wireless network for your guests to share the hotspot / remote wireless network you are connected to. It can either be password protected with a wireless key or preferably an open SSID which your guest can easily join to.
The Guest Wifi is isolated from your private network, meaning any devices joining on the Guest Wifi SSID will not able to access or see your devices connected on your private wireless network or access to the Ezhotspot EXtender.
Enter a Guest SSID which your guests can connect to and choose wireless key required if you prefer your guests to enter a wireless key to join to your Guest Wifi.
Tor Network
This menu allows you to enable the Tor network on the Ezhotspot Extender
 |
|

Current Public IP : 123.123.123.1 |
|
This informational menu opens up a new window to Tor website to check if you are connected to the Tor network
check tor status
Tor® is a registered trademark of The Tor® Project, Inc; a non-profit corporation organized to research and develop the Tor® anonymity software and network. Tor® aims to conceal its users' identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation of onion routing, which encrypts and then randomly bounces communications through a network of relays run by volunteers around the globe.
The Ezhotspot Extender has a easy 1 click to let you enjoy anonymous internet browsing using Tor®. The Tor® network disguises your identity by moving your traffic across different Tor servers, and encrypting that traffic so it isn't traced back to you.
Now, you are in The Netherlands, the next moment you are in France or can be anywhere else in the world!
The Ezhotspot Extender has a easy 1 click, where you can start to enjoy anonymous browsing. If you are connected to a public hotspot running on a captive portal, please select public network before proceeding.
If you support Internet anonymity, consider contributing to The Tor® Project as a donor, running a relay or volunteering as a developer.
Disclaimer: Tor® Network is not supported by ezWifi or vice versa. Usage of The Tor® Network is at own discretion, DOs & DONs of Tor® Network policy, Internet social etiquette and OF USE AS IT IS condition.
Tor® is a trademark of The Tor® Project. This product is produced independently from the Tor® anonymity software and carries no guarantee from The Tor® Project about quality, suitability or anything else.
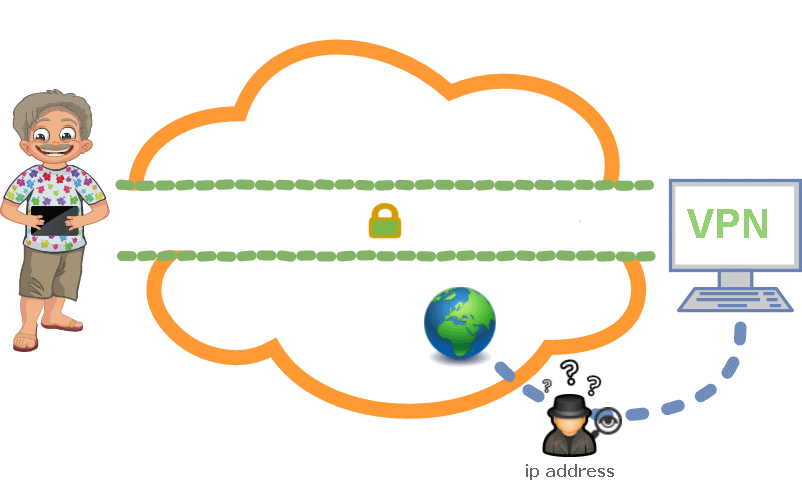
OpenVPN
OpenVPN uses client-server connection to provide secure communication between the client and the internet. The server side is directly connected to the internet and client connects with the server and ultimately connects with the internet indirectly. On the internet, the client is shown as the server itself and it uses the physical location and other attributes of server that means the identity of client is perfectly hidden.
OpenVPN uses OpenSSL for encryption and authentication process and it can use UDP as well as TCP for transmission. Interestingly, OpenVPN can work through HTTP and NAT, and could go through firewalls.
In Short, OpenVPN is popular because of numerous reasons, but mainly it : -
- hides your original IP address
- allows you to access websites blocked by your local Internet Service Provider and Hotspot providers
- allows you to watch a local TV program when you are in a foreign region
- can work over ports 80/443 which public websites normally listen on and which Hotspot Providers are not able to *block
* An extra premium is required with some hotel hotspot providers to make a L2TP/IPSEC connection to your corporate office/home, for example.
OpenVPN uses either pre-shared key, combination of user name and passwords or certificate to authenticate peers connected via OpenVPN and its major characteristics are its extensive support and strong features.

CLIENT |

SERVER |
PPTP/L2TP
Note: The PPTP/L2TP will be deprecated in future firmware. It is strongly recommended to use the improved OpenVPN , which offers more possibility and security. OpenVPN is currently the deFacto standard in Virtual Private Networks.
PPTP stands for "Point-to-Point Tunneling Protocol." PPTP is a networking standard for connecting to virtual private networks, or VPNs. VPNs are secure networks that can be accessed over the Internet, allowing users to access a network from a remote location. This is useful for people who need to connect to an office network from home or access their home computer from another location.
In Short, PPTP is useful because : -
- hides your original IP address
- allows you to access websites blocked by your local Internet Service Provider and Hotspot providers
- allows you to watch a local TV program when you are in a foreign region
The "point-to-point" part of the term refers the connection created by PPTP. It allows one point (the user's computer) to access another specific point (a remote network) over the Internet. The "tunneling" part of the term refers to the way one protocol is encapsulated within another protocol. In PPTP, the point-to-point protocol (PPP) is wrapped inside the TCP/IP protocol, which provides the Internet connection. Therefore, even though the connection is created over the Internet, the PPTP connection mimics a direct link between the two locations, allowing for a secure connection.
L2TP stands for Layer Two Tunneling Protocol is an extension of the Point-to-Point Tunneling Protocol (PPTP) used by an Internet service provider (ISP) to enable the operation of a virtual private network (VPN) over the Internet. L2TP merges the best features of two other tunneling protocols: PPTP from Microsoft and L2F from Cisco Systems. The two main components that make up L2TP are the L2TP Access Concentrator (LAC), which is the device that physically terminates a call and the L2TP Network Server (LNS), which is the device that terminates and possibly authenticates the PPP stream.
DDNS
DDNS is a service that maps internet domain names to IP addresses and allow you to access your home computer from anywhere in the world.
DDNS serves a similar purpose to Internet's Domain Name System (DNS) in such that DDNS lets you to host a web or VPN server advertise a public name instead of numbers.
Further, unlike DNS that only works with static IP addresses, DDNS is designed to also support dynamic (changing) IP addresses, such as those assigned by a DHCP server. That makes DDNS a good fit for home networks, which normally receive dynamic public IP addresses from their internet provider. The result is that if your IP address changes, your domain name will adapt to the new IP address.
To use DDNS on the Ezhotspot Extender, you have to sign up at http://freedns.afraid.org/signup/?plan=starter with a free starter account. Only your email is needed for verification and a confimration will be sent to your email after registering. Check your spam boxes if you do not receive the confirmation. (Though if you like the service, you can make a donation at your discretion)
After your confirmation, you can login to create your desirable domain name and obtaining the API which you will need to enter these 2 information in the EZhotspot Extender. EZhotspot EXtender will then periodically check if your public IP has changed and upate to freedns.afraid.org, which takes 60 minutes to effect.

